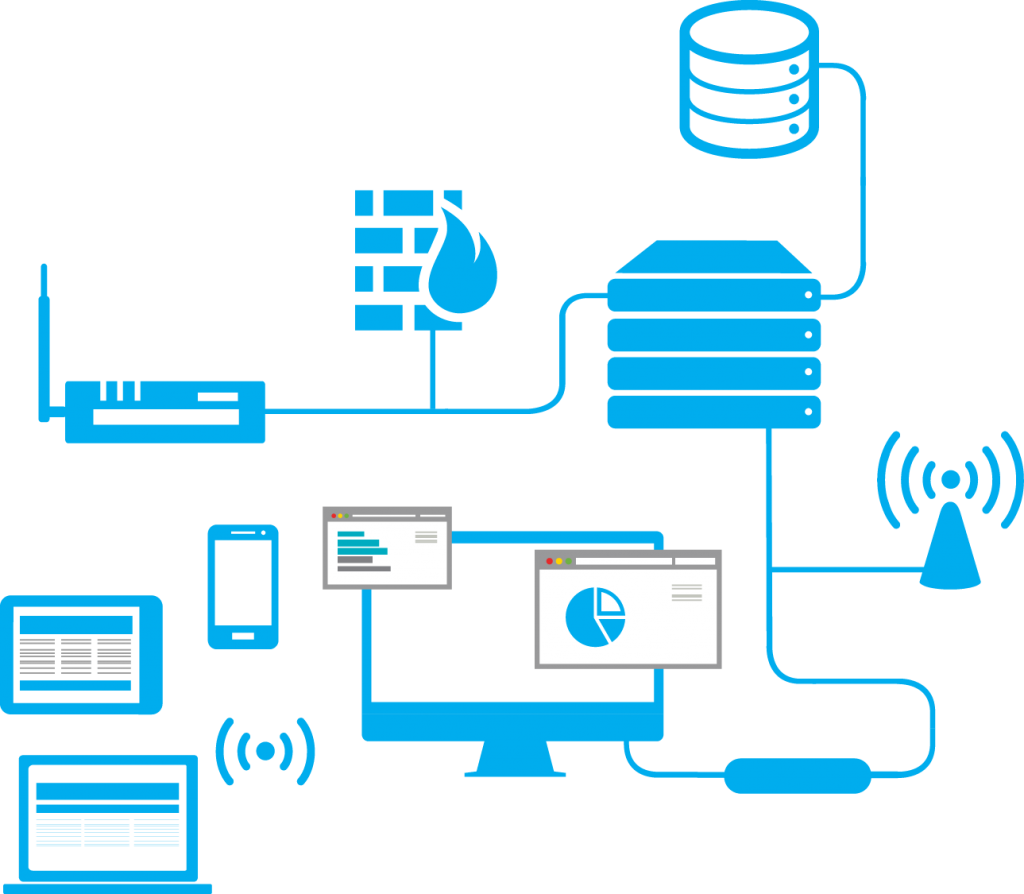
Explore a selection of my recent projects, including software development, networking solutions, and technical innovations.
Summit Care Medical Clinic Network Architecture Master Blueprint
This network infrastructure report presents a complete modernization blueprint for Summit Care Medical Clinic, outlining the strategy, architecture, deployment planning, security controls, documentation standards, and recovery design used to transform a small office healthcare environment into a more structured enterprise-grade infrastructure. Summit Care Medical Clinic is used here as a fictionalized organization so the full workflow can be presented clearly while keeping actual production identities and sensitive organizational details private.
Enterprise Network Upgrade Hybrid Cloud, Security & Recovery by Sidiq Daniel
Project Overview
A full-length technical report covering the planning, research, build standards, implementation approach, and operational structure behind the Summit Care network upgrade.
Report Focus
Focused on architecture, deployment, hybrid identity, segmentation, cybersecurity, documentation, and disaster recovery across one unified healthcare infrastructure workflow.
Table of Contents
- Executive Summary
- Introduction & Project Intent
- Company Objectives & Gap Analysis
- Research & Development
- Assets, Inventory & Procurement
- Documentation, Diagrams & Topologies
- Infrastructure Deployment & Configurations
- Hybrid Cloud Infrastructure & Scalability
- Network Segmentation, VLANs & Subnetting
- Cybersecurity, Data Protection & HIPAA Compliance
- Disaster Recovery & Backup Plan
- Conclusion
Executive Summary
This report documents a fictionalized healthcare infrastructure upgrade used to demonstrate real implementation workflow, engineering thought process, and operational design maturity. The scenario centers on transforming a small office medical environment into a more production-ready enterprise network through structured planning, standardization, hybrid identity, segmented networking, stronger monitoring, and layered recovery design.
It demonstrates end-to-end infrastructure thinking across research, procurement, documentation, deployment, Microsoft hybrid identity, network segmentation, cybersecurity, and disaster recovery, while presenting the work in a sanitized, portfolio-safe format for professional review.
Introduction & Project Intent
Summit Care Medical Clinic is presented here as a mock healthcare organization used to demonstrate a real-world infrastructure upgrade workflow in a presentation-safe format. The technical approach, engineering logic, deployment sequence, documentation methods, and support standards reflect practical infrastructure work, while the organization name and identifiers were intentionally fictionalized so the report can be shared publicly for educational and professional review.
The core challenge was to take a small office medical environment with limited standardization, uneven security controls, minimal centralized management, and basic network architecture, then redesign it into a more resilient, supportable, segmented, and enterprise-style production environment.
Company Objectives & Gap Analysis
The target environment introduced Windows domain services, identity-based wireless access, stronger segmentation, hybrid Microsoft identity, standardized endpoints, recovery planning, role-based access, cleaner documentation, and a much more supportable operational baseline.
- Replace flat small-office networking with segmented enterprise-style architecture.
- Standardize user desktops and laptops for easier provisioning and scaling.
- Introduce Active Directory, DNS, DHCP, NPS/RADIUS, and centralized Windows identity.
- Replace shared wireless passwords with WPA2-Enterprise and identity-backed wireless access.
- Support remote work, VPN access, Teams collaboration, and future office growth.
- Improve documentation, asset visibility, backup readiness, and HIPAA-aware administration.
Research & Development
The research phase evaluated hardware platforms, cloud ecosystems, virtualization options, software choices, licensing paths, VPN models, support tooling, and staff readiness before procurement and deployment began.
- Cisco and Ubiquiti were compared for routing, switching, controller management, and long-term scalability.
- Google Workspace and Microsoft were compared, with Microsoft selected for better alignment with Windows domain services, Entra synchronization, Teams, OneDrive, and role-based cloud administration.
- Proxmox, Hyper-V, and VMware were reviewed, with Proxmox chosen as the practical fit for cost, familiarity, and flexible virtualization.
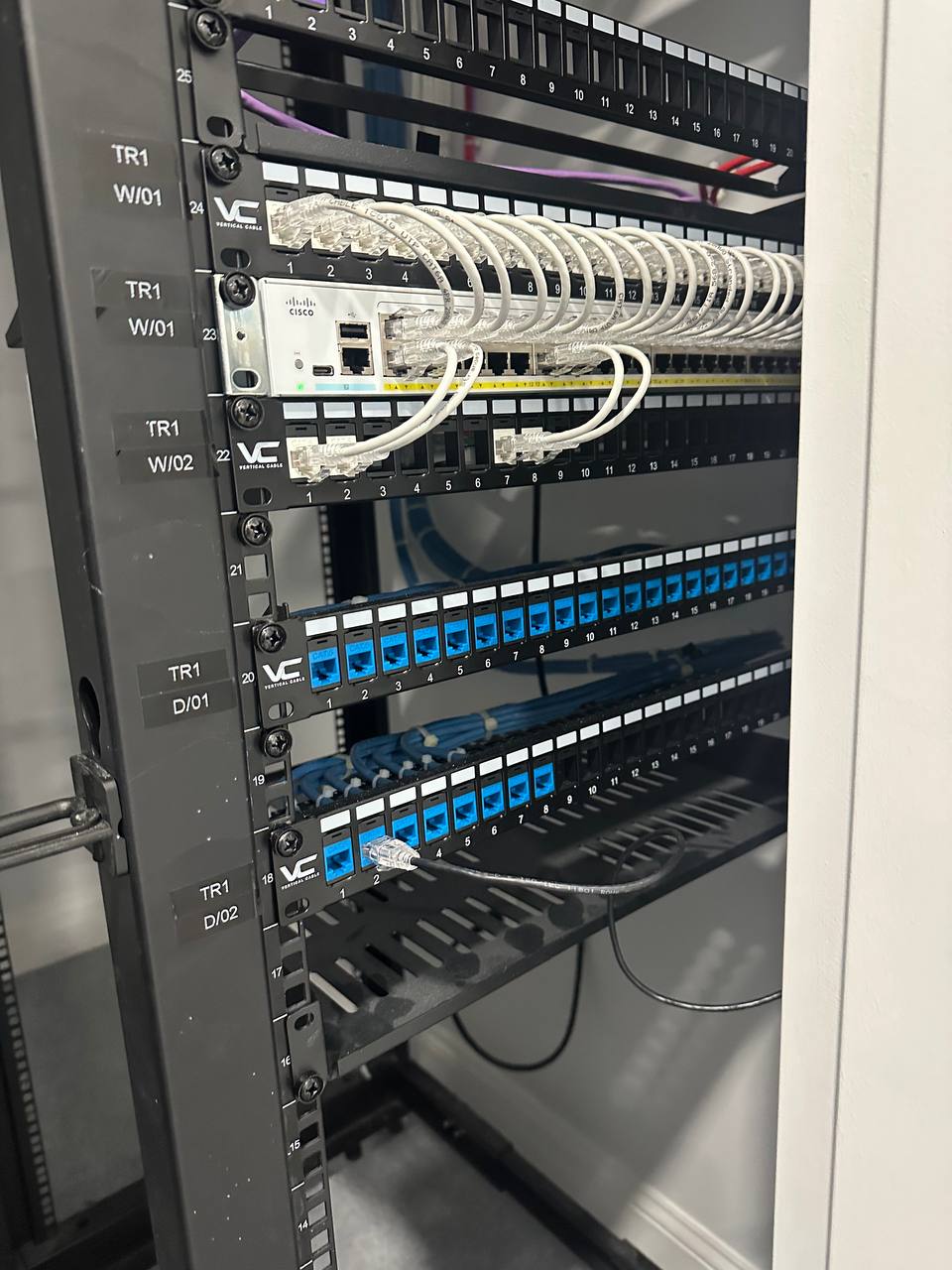
Assets, Inventory & Procurement
Asset tracking begins in Google Sheets stored in Google Drive as the early source of truth. Device name, model, quantity, serial information, ownership, location, status, and licensing notes are recorded there before later documentation is copied into broader operational repositories.
- Dell PowerEdge R740XD server for core virtualization and service hosting.
- Dell OptiPlex desktops and Dell Inspiron laptops for endpoint standardization.
- Cisco ASA firewall, Cisco router, Cisco CBS 1300 switching, and Ubiquiti access points.
- Synology NAS and UPS integrated into the backup and recovery posture.
Documentation, Diagrams & Topologies
Documentation is maintained in a practical multi-location repository model using Office Drive or OneDrive, local office repositories, and Synology NAS copies to maintain a three-location documentation posture.
- Asset inventories, device location records, and labeling references.
- Hostname, IP address, VLAN, subnet, server role, and application role documentation.
- Firewall rules, VPN settings, DHCP reservations, and wireless standards.
- Diagram families covering physical, logical, virtual, VPN, hybrid cloud, and management topology views.
Infrastructure Deployment & Configurations
Deployment was based on golden baselines, repeatable build standards, and documented administration so the environment would remain supportable, auditable, and scalable after go-live.
- Proxmox deployed on the Dell PowerEdge R740XD as the type-1 hypervisor.
- Windows Server 2022 VM providing Active Directory, DNS, DHCP, and NPS/RADIUS.
- Additional Linux VPN VM for software-based backup remote access.
- Windows 11 endpoints provisioned from standardized USB media, joined to Active Directory, and brought under Group Policy.
- Cisco devices administered over SSH with exported configurations retained across server, NAS, and cloud repositories.
Hybrid Cloud Infrastructure & Scalability
The hybrid cloud approach is centered on Microsoft identity and service integration rather than full cloud migration. The local server environment remains the operational anchor while Entra and Microsoft 365 extend identity, password management, collaboration, licensing, and cloud-side user administration.
- Microsoft Entra Connect deployed for directory synchronization.
- Password hash sync, password writeback, SSPR, and MFA enabled.
- Microsoft 365 apps, Teams, OneDrive, and related cloud services tied into the same sign-in workflow.
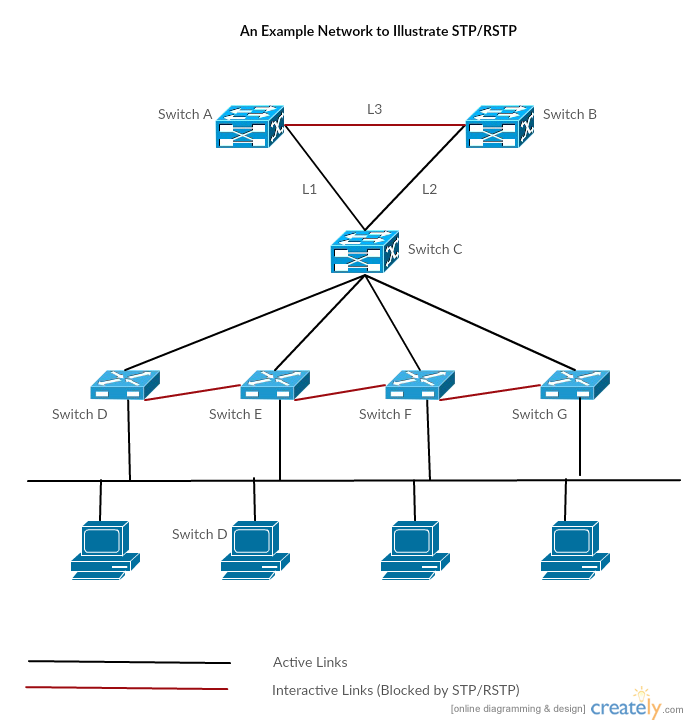
Network Segmentation, VLANs & Subnetting
Segmentation separates the upgraded Summit Care environment from a simpler flat office network. The design uses the private range 10.7.0.0/16 and breaks it into role-based /24 subnets for endpoints, internal servers, public services, application data, guest Wi-Fi, cameras, VPN access, voice, management, and out-of-band server management.
- 802.1Q trunking across Cisco switching for multiple VLANs.
- Inter-VLAN routing controlled through the routed and firewall layer.
- Cisco ASA ACLs defining which subnets may communicate and under what conditions.
- Windows firewall and host controls adding another enforcement layer.
Cybersecurity, Data Protection & HIPAA Compliance
Security is layered into the design rather than added afterward. The architecture combines segmentation, identity-backed wireless access, role-based controls, Microsoft MFA, logging, DLP, firewalling, secure administration, SNMP monitoring, and recovery-aware documentation practices.
- WPA2-Enterprise wireless tied to Windows NPS/RADIUS.
- Organization-wide MFA across Microsoft-connected services and management portals.
- SSH private key or certificate-based administration for Cisco and Linux systems.
- Primary Cisco firewall VPN with Linux-based backup VPN for continuity.
- HIPAA-aware software and cloud-service review before adoption.
Disaster Recovery & Backup Plan
Recovery follows a practical 3-2-1 backup model supported by documentation, exported configurations, UPS-backed continuity, and rebuild baselines.
- Primary on-prem copy retained on the local server environment.
- Secondary local copy retained on a Synology NAS.
- Offsite or cloud-connected copy retained through OneDrive and related managed storage paths.
- Nightly PowerShell-driven backups running on a documented schedule.
- Config exports retained across server, NAS, and cloud locations.
Conclusion
This Summit Care Medical Clinic master report captures a complete network modernization workflow from planning to recovery readiness. Presented through a fictionalized healthcare organization, it documents how a small office environment can be redesigned into a more structured enterprise-style production model through stronger documentation, standardized deployments, hybrid identity, segmented networking, monitored security controls, and layered recovery design.
As a portfolio document, it is intended to show design reasoning, implementation logic, and infrastructure leadership in a form detailed enough to demonstrate real technical depth while remaining safe to share for interviews, professional review, and resume support.
Summit Care Centralized Identity & Hybrid Network Architecture
This master report presents a mock enterprise architecture for Summit Care Medical Clinic. It shows how Azure, Microsoft Entra ID, on-premises Active Directory, one-way trusts, regional VPN hubs, Azure VPN Gateway, GPO logon restrictions, SSO, MFA, password hash sync, password writeback, RBAC, and HIPAA-aligned safeguards can support secure multi-campus healthcare operations without using any real company information.
SCGLOBAL.LOCAL, SUMMITCARE.ORG, master-leaf AD, hub-and-spoke VPN, and HIPAA safeguards
Project Goal
Centralize global identity in Azure while preserving each campus as an independent local Active Directory environment with its own users, groups, GPOs, resources, and operational boundaries.
Key Rule
Tier A global users can authenticate across approved campuses. Tier B local users stay restricted to their home campus through domain design and GPO logon controls.
Contents
- Overview & Purpose
- Identity Architecture
- Network & IP Scheme
- Entra Hybrid Sync Build
- GPO Logon Restrictions
- HIPAA, Risks & Governance
- Final Summary
Overview & Purpose
Summit Care Medical Clinic needs centralized identity management, secure cross-campus access for global staff, local autonomy for individual clinic domains, and a private WAN-like network built with VPNs. Azure hosts the central identity authority and provides the cloud security control plane.
- Centralize authentication and identity governance.
- Keep campus Active Directory environments independent.
- Allow Tier A global users to authenticate at approved campuses.
- Restrict Tier B local users to their assigned campus.
- Use regional hub-and-spoke VPN routing instead of direct campus-to-campus communication.
- Enable SSO, MFA, Conditional Access, password hash sync, password writeback, RBAC, and audit logging.
Identity Architecture
The design uses a master-leaf Active Directory model. SCGLOBAL.LOCAL is hosted in Azure as the central identity authority for Tier A global users, while summitcare.org in Microsoft Entra ID provides cloud identity, Microsoft 365 SSO, MFA, Conditional Access, password writeback, RBAC, and audit visibility.
- East leaf domains: SCQNS.LOCAL, SCMAN.LOCAL, SCBKLYN.LOCAL, SCNWRK.LOCAL.
- West leaf domains: SCPHX.LOCAL, SCDAL.LOCAL, SCDEN.LOCAL, SCLA.LOCAL.
- Campus domains trust SCGLOBAL.LOCAL for Tier A authentication referrals.
- No direct campus-to-campus trust is created, preserving local isolation.
Tier A global users authenticate where authorized through one-way trusts, while Tier B local users remain restricted to their home campus. Privileged administrators are protected with MFA, RBAC, least-privilege access, and audit logging.
Network & IP Scheme
The network design uses a hub-and-spoke VPN model with Azure at 10.90.0.0/16, the East region at 10.91.0.0/16, and the West region at 10.92.0.0/16.
- Azure identity subnet: 10.90.10.0/24 for SCGLOBAL domain controllers and sync services.
- Azure gateway subnet: 10.90.254.0/27 for Azure VPN Gateway.
- East region hub in Queens with Manhattan, Brooklyn, and Newark as spokes.
- West region hub in Phoenix with Dallas, Denver, and Los Angeles as spokes.
- Campus traffic follows Campus to Meraki VPN, Meraki VPN to regional hub, regional hub to Azure VPN Gateway, then Azure to SCGLOBAL services.
Each campus DNS server uses conditional forwarders for SCGLOBAL.LOCAL, VPN and firewall rules allow required Kerberos, LDAP, and DNS traffic, and no campus creates a direct trust with another campus.
Microsoft Entra Hybrid Identity Sync Build
The Entra hybrid sync build standard centers on healthy Active Directory, verified cloud identity, aligned UPNs, and a dedicated sync server.
- Run
dcdiag /v and repadmin /replsummary to validate AD health.
- Verify summitcare.org in Microsoft Entra ID.
- Align UPNs so users sign in as [email protected] instead of local-only suffixes.
- Build SC-SYNC01 as a dedicated, domain-joined sync server at 10.90.10.20.
- Deploy Microsoft Entra Connect Sync with customized settings, Password Hash Sync, Seamless SSO, and password writeback where supported.
- Filter synced OUs to exclude stale, disabled, service, or lab objects.
Operational checks include delta and initial sync cycles, Synchronization Service Manager review, and validation of Microsoft 365 sign-in, Teams, Outlook, MFA, and password reset behavior.
GPO Logon Restrictions
Summit Care uses GPO deny-local-logon controls to prevent local Tier B users from signing into workstations outside their assigned campus. This is separate from the Tier A global authentication model.
- Create cross-domain deny groups such as Deny_SCQNS_Login.
- Add targeted foreign domain user groups into those deny groups.
- Create and link workstation-focused GPOs such as Deny SCQNS Logon To SCBKLYN.
- Use
gpupdate /force and testing to validate restrictions before rollout.
- Do not deny Domain Admins, Enterprise Admins, local Administrators, SYSTEM, or emergency break-glass accounts.
HIPAA, Risks & Governance
Security and governance controls in Azure and Entra support unique user identification, person or entity authentication, access control, audit logging, and faster offboarding.
- MFA, Password Hash Sync, Conditional Access, and password policy reduce sign-in risk.
- RBAC, groups, app assignment, and Conditional Access enforce least privilege.
- Entra audit logs, sign-in logs, and role history support evidence and review.
- Disable or delete workflows, session revocation, and sync validation improve access termination.
Potential blockers include regional hub failure, DNS resolution issues, VPN Gateway bottlenecks, latency to remote regions, and dirty Active Directory before sync. The design addresses these with HA Meraki pairs, conditional forwarders, proper gateway sizing, balanced Azure region placement, and pre-sync AD cleanup.
Final Summary
The final Summit Care architecture creates centralized cloud control without collapsing every clinic into one flat trust model. SCGLOBAL.LOCAL in Azure acts as the master identity authority, summitcare.org in Microsoft Entra ID provides cloud governance, regional VPN hubs provide private connectivity, and campus domains retain local autonomy.
Tier A users can authenticate where authorized, Tier B users stay local, and Azure with Entra adds SSO, MFA, Conditional Access, password hash sync, password writeback, RBAC, audit logs, and HIPAA-aligned evidence. The result is a secure, segmented, scalable design ready to support many Summit Care Medical Clinic locations.
Summit Care Medical Clinic Cyber Threat Analysis & Risk Assessment
A complete rebranded security portfolio document combining the Summit Care healthcare network blueprint with the prior cyber threat analysis project. This report presents a realistic, sanitized assessment of penetration testing, vulnerability management, HIPAA-aware controls, third-party risk, audit evidence, incident response, and remediation planning for a mock medical clinic network.
Penetration Testing, Risk Assessments, and HIPAA Security Rule Alignment by Sidiq Daniel
- 10.7.0.0/16 sanitized Summit Care private network model.
- 6 NIST CSF 2.0 functions used for mapping.
- 12 representative findings and audit scenarios.
- 90 days priority remediation roadmap.
Document Index
- Executive Summary
- Engagement Profile
- Summit Care Environment
- Methodology
- Asset & Data Classification
- Threat Model
- Penetration Testing Narrative
- Risk Register
- HIPAA & Compliance Alignment
- Third-Party Audit Program
- Monitoring & Routine Auditing
- Incident Response & Recovery
- Remediation Roadmap
- Evidence & References
Executive Summary
This master report reframes the existing Summit Care Medical Clinic network architecture into a cybersecurity assessment deliverable. The goal is to show the full security workflow: understanding the business environment, identifying critical healthcare assets, testing realistic attack paths, ranking risk, recommending controls, documenting HIPAA-aware safeguards, and preparing the organization for continuous improvement.
Summit Care is a fictionalized healthcare clinic used to protect real client identities while preserving the technical substance of infrastructure and security work. The environment includes segmented clinical, administrative, billing, voice, wireless, and guest networks; Microsoft identity services; endpoint standards; network monitoring; backup planning; and hybrid cloud collaboration through Microsoft 365 and Entra-connected services.
- High: top residual risk is exposed management and weak administrative access paths.
- Critical: protected health information and billing systems are crown-jewel assets.
- Moderate: overall maturity after segmentation, MFA, backups, and monitoring baseline.
- Continuous: quarterly testing and recurring audit cadence recommended.
Portfolio positioning: this report demonstrates cybersecurity analysis, risk assessment, audit documentation, penetration testing workflow, technical writing, healthcare compliance awareness, and security governance in one organized master document.
Engagement Profile
The assessment was modeled as an authorized internal security review for a small healthcare office preparing for stronger network governance and HIPAA Security Rule alignment. Testing scenarios are written as controlled simulations and sanitized examples, not instructions for unauthorized activity.
In Scope
- Clinical systems, EMR-facing servers, billing applications, admin workstations, and shared services.
- Firewall rules, VLAN segmentation, wireless access, VPN access, DNS, DHCP, AD, NPS/RADIUS, and endpoint posture.
- HIPAA Security Rule safeguards, NIST CSF 2.0 mapping, incident response, backup readiness, and third-party risk.
Out Of Scope
- Unsafe production exploitation, destructive testing, denial-of-service activity, and live PHI exposure.
- Unapproved password harvesting, persistence deployment, or changes to patient-care systems during business hours.
- Real patient names, production credentials, public IP addresses, vendor secrets, or client-identifying data.
Summit Care Environment
Summit Care's mock environment represents a small but realistic medical clinic where clinicians need fast access to patient records, billing staff handle financial workflows, administrators manage scheduling and documents, and IT must protect the network without slowing down patient care.
Representative Segmentation Model
- Clinical / EMR - 10.7.10.0/24: ePHI, EMR access, charting stations.
- Billing / Finance - 10.7.20.0/24: claims, payment workflows, financial records.
- Administration - 10.7.30.0/24: scheduling, HR, and general office workstations.
- Server / Services - 10.7.40.0/24: AD, DNS, DHCP, NPS/RADIUS, file services, and monitoring.
- Voice / IoT - 10.7.50.0/24: VoIP phones, printers, cameras, and appliance-like devices.
- Guest Wireless - 10.7.90.0/24: patient and visitor internet-only access.
Methodology
The methodology combines the older cyber threat analysis workflow with the newer Summit Care infrastructure design. It follows a defensible path: identify assets, scan and validate vulnerabilities, test attack paths safely, rate risk, document control gaps, and verify remediation.
- Discovery and asset inventory.
- Threat modeling for phishing, stolen credentials, exposed remote access, unpatched services, ransomware, and vendor compromise.
- Vulnerability assessment using Nmap, Nessus/OpenVAS-style scanning, configuration review, log review, and manual validation.
- Controlled penetration testing across external, internal, wireless, web application, and privileged-user scenarios.
- Risk rating based on likelihood, impact, data sensitivity, exploitability, and compensating controls.
- Remediation and retest with owners, timelines, and residual risk documentation.
Frameworks represented include NIST CSF 2.0, HIPAA Security Rule safeguards, OWASP testing concepts, CIS-style hardening practices, and internal risk scoring.
Asset & Data Classification
Security decisions were prioritized around the systems that store, process, or provide access to ePHI, billing records, user identities, network controls, and recovery data.
- EMR / Clinical Workstations: critical due to patient-care disruption and privacy risk.
- Billing System / Claims Workflow: high impact due to financial data exposure and fraud risk.
- Active Directory / Entra Identity: critical because compromise enables broad lateral movement.
- Firewall, Switches, Wireless Controllers: high impact due to routing and segmentation exposure.
- NAS / Backup Repository: critical because ransomware resilience depends on backup integrity.
- VoIP, Printers, Cameras, IoT: medium impact with pivot risk and privacy-adjacent exposure.
Threat Model
The highest-value risks were treated as business scenarios that could affect patient care, PHI confidentiality, billing operations, staff productivity, and regulatory posture.
- Scenario A - Credential Theft To EMR Access: phishing leads to attempted cloud, VPN, or remote desktop access.
- Scenario B - Ransomware Through Unpatched Endpoint: code execution leads to lateral movement and operational disruption.
- Scenario C - Billing Portal SQL Injection: unsafe input handling risks financial and compliance exposure.
- Scenario D - Vendor Remote Support Misuse: third-party support tooling introduces inherited attack paths.
Penetration Testing Narrative
Penetration testing was positioned as validation of risk, not a hunt for dramatic exploits. The test plan measured whether Summit Care's controls could prevent, detect, and contain realistic attack paths.
Testing Phases
- Reconnaissance of exposed services, email patterns, DNS records, VPN entry points, and internal subnets.
- Vulnerability validation against versions, patch levels, configuration files, and manual checks.
- Web application testing for injection risk, authentication weakness, session handling, and error leakage.
- Internal segmentation testing across admin, billing, clinical, IoT, and guest networks.
- Privileged access review covering local admin, domain admin exposure, shared credentials, service accounts, and remote management paths.
Representative Findings
- PT-01: Domain Admin Exposure On Workstations - Critical
- PT-02: Weak SSH / Network Device Management - High
- PT-03: Billing Portal Injection Risk - High
- PT-04: Guest Network Egress And Discovery Noise - Medium
Risk Register
Risks were scored using impact and likelihood, with extra weight added for ePHI, identity systems, patient-care availability, and whether the issue could be chained with another weakness.
- R-01: privileged credentials exposed on normal endpoints.
- R-02: unpatched EMR-supporting web service.
- R-03: billing portal injection weakness.
- R-04: inconsistent MFA and conditional access across VPN and cloud tools.
- R-05: third-party remote support lacks complete audit evidence.
- R-06: backup restore testing not fully documented.
- R-07: default or weak SNMP strings on network devices.
- R-08: user phishing susceptibility in finance and scheduling groups.
HIPAA & Compliance Alignment
The HIPAA Security Rule requires regulated entities to protect electronic protected health information with appropriate administrative, physical, and technical safeguards. For this mock clinic, the practical compliance focus is risk analysis, access control, audit controls, integrity, transmission security, workforce security, contingency planning, and vendor oversight.
- Administrative Safeguards: security responsibility, access review, workforce training, incident response, and vendor review.
- Physical Safeguards: server closet control, UPS protection, workstation placement, visitor separation, and device inventory.
- Technical Safeguards: unique user IDs, MFA, role-based access, firewall segmentation, encryption, audit logs, and endpoint protection.
- Risk Analysis / Risk Management: asset inventory, risk register, scan summaries, remediation roadmap, and retest documentation.
- Business Associate / Vendor Oversight: BAA tracking, vendor access lists, remote support review, and questionnaires.
This report supports a HIPAA-aware security program, but it is not a legal opinion or formal compliance certification.
Third-Party Audit Program
Healthcare clinics rely heavily on vendors such as EMR platforms, billing services, VoIP providers, MSPs, backup platforms, cloud storage, email security, internet service providers, and remote support tools. Each vendor can become part of the clinic's attack surface.
- Review whether the vendor handles ePHI and whether a Business Associate Agreement is required.
- Require named accounts, MFA, and least-privilege support roles for remote access.
- Review breach notification terms, data retention, encryption, backup, and subcontractor language.
- Track corrective actions, due dates, vendor owners, and risk acceptance decisions.
Monitoring & Routine Auditing
The operations model makes security repeatable: collect logs, check baselines, review access, scan for vulnerabilities, and prove that backups and controls still work.
- Daily: review critical alerts, backup status, endpoint protection, failed admin logons, and firewall deny spikes.
- Weekly: review vulnerability deltas, firewall changes, email risk events, VPN activity, and privileged group changes.
- Monthly: patch servers and network devices, review inactive accounts, validate guest Wi-Fi separation, and export configs.
- Quarterly: run access recertification, restore-test backups, tabletop incident response, vendor review, and risk register updates.
Log sources to centralize include firewall and VPN events, Active Directory and Entra identity events, endpoint protection alerts, and EMR or billing application logs.
Incident Response & Recovery
Summit Care's response model is built around detection, containment, eradication, recovery, communication, and lessons learned.
- Ransomware Playbook: isolate affected VLANs, preserve evidence, disable suspect accounts, validate backups, and restore priority services.
- Lost Device / ePHI Exposure: confirm encryption and MDM status, remote lock or wipe, assess affected data, and trigger privacy review.
- Vendor Account Compromise: disable vendor access, collect logs, rotate credentials, verify touched systems, and require corrective action.
Recovery Priorities
- Identity, DNS, DHCP, and network core.
- EMR and clinical workstations.
- Billing, file shares, printing, and voice.
- Guest Wi-Fi, nonessential IoT, and secondary services.
Remediation Roadmap
The roadmap translates findings into practical work that a clinic can actually execute.
- 0-30 Days: enforce MFA, remove shared admin accounts, patch critical systems, isolate guest Wi-Fi, review vendor access, and confirm backup alerts.
- 31-60 Days: implement privileged access workstations, database least privilege, SNMPv3, centralized logging, phishing reporting, and secure configuration baselines.
- 61-90 Days: perform retest, restore-test backups, complete HIPAA safeguard evidence binder, run incident response tabletop, and complete third-party risk reviews.
- Ongoing: quarterly vulnerability scans, annual penetration tests, monthly access review, continuous monitoring, policy refresh, and leadership risk review.
Evidence & References
The final security portfolio should include enough evidence for a reviewer to understand the work without exposing live secrets.
- Sanitized network diagram and VLAN map.
- Asset inventory and data classification sheet.
- Vulnerability scan summary and false-positive notes.
- Penetration testing scope memo and executive findings.
- Risk register with owners, due dates, and retest status.
- HIPAA safeguard matrix and audit evidence checklist.
- Third-party or vendor risk questionnaire summary.
- Incident response tabletop and backup restore test report.
Key deliverables include the Cyber Threat Analysis and Risk Assessment Master Report, penetration testing narrative and findings, HIPAA-aware control alignment, third-party audit framework, a 30/60/90-day remediation roadmap, and an ongoing monitoring and audit cadence.
DHCP Failover Project Workflow
A condensed infrastructure report for Summit Care Medical Clinic focused on Windows Server 2022 DHCP, Cisco ASA emergency DHCP failover, Proxmox virtualization, DNS dependency planning, and recovery operations. The purpose of the project is to improve uptime, redundancy, and service continuity so the office can stay as operational as possible even if the primary DHCP server fails.
Dell PowerEdge R740xd, Proxmox type-1 hypervisor, Windows Server 2022 DHCP, and Cisco backup DHCP
Purpose & Goal
Build a supportable DHCP continuity design that reduces the chance of a single Windows service failure interrupting address delivery for office workstations, front-desk systems, and other wired clinic devices.
Design Principle
Keep Windows Server as the primary DHCP authority, use Cisco only as an emergency path during outage conditions, and return cleanly to the normal service model after recovery.
Table of Contents
- Executive Summary
- Overview & Strategy
- Architecture & Configuration
- Operations & Recovery
- Risk, Governance & Conclusion
Executive Focus
This report presents Summit Care Medical Clinic as a realistic healthcare infrastructure scenario focused on one high-value objective: keep internal office devices receiving valid IP configuration even if the primary Windows DHCP service becomes unavailable, so the office can remain as operational as possible during outage conditions.
- Primary Service Model: Windows Server 2022 virtual machine on Proxmox acts as the normal DHCP and DNS authority for the internal office LAN.
- Emergency Continuity Model: if the domain controller at 10.40.10.10 stops responding, the Cisco edge device enables an emergency DHCP pool so wired devices can still obtain an address, default gateway, and basic external connectivity.
- Failback Discipline: when the Windows server returns and health checks stabilize, the Cisco backup pool is disabled so the clinic returns to the normal primary service model.
Important design note: this is not native Microsoft DHCP failover between two Windows servers. It is a layered continuity design that uses a Cisco backup service for outage coverage while preserving Windows as the primary DHCP authority.
Overview & Strategy
The goal is to improve uptime, reduce the operational impact of DHCP service failure, and keep the office infrastructure usable during an outage window. Rather than replacing Windows with Cisco, the strategy preserves Windows as the richer management platform while giving the clinic a practical emergency DHCP bridge on the network edge.
- Reduce the chance that a single Windows DHCP outage stops new devices from joining the LAN.
- Support near-continuous address availability for front-desk, nursing, office, and wired workstation users.
- Preserve administrative clarity by automatically falling back to Windows DHCP after recovery.
- Support a more resilient office infrastructure posture built around uptime, redundancy, and cleaner failover recovery.
Resilience snapshot: primary DHCP availability target 96%, fallback service coverage 82%, administrative visibility during failover 74%, and internet continuity for wired devices 88%.
Summit Care Blueprint Snapshot
- Dell PowerEdge R740xd: stable enterprise hardware base for critical infrastructure VMs.
- Proxmox VE: type-1 hypervisor supporting better recovery posture, snapshots, and host-level organization.
- Windows Server 2022: primary DHCP and DNS platform with domain-aware administrative depth.
- Cisco edge firewall/router: emergency DHCP backup supplying temporary lease continuity when the primary server is unavailable.
Architecture & Configuration
The internal office LAN uses 10.40.10.0/24. Windows Server 2022 owns the normal lease range at 10.40.10.100 through 10.40.10.199, while Cisco is staged with a separate emergency-only range at 10.40.10.210 through 10.40.10.230. The default gateway remains 10.40.10.1, and the domain controller health-check IP remains 10.40.10.10.
- Infrastructure exclusion range: 10.40.10.1 through 10.40.10.99 for statics, printers, switches, and servers.
- Windows primary pool: 10.40.10.100 through 10.40.10.199.
- Cisco emergency-only pool: 10.40.10.210 through 10.40.10.230.
- Primary DNS: 10.40.10.10 for internal resolution and domain-aware operation.
Windows Server DHCP Manager Implementation
- Build the Windows Server 2022 VM on Proxmox and assign 10.40.10.10 as a static address.
- Install the DHCP Server role, complete post-install steps, and authorize the service in Active Directory.
- Create the IPv4 office scope for 10.40.10.0/24 and define the primary pool.
- Add exclusions for infrastructure space, set router 10.40.10.1, DNS 10.40.10.10, lease timing, and reservations.
- Activate the scope and verify a test client successfully receives a lease from Windows before backup logic is introduced.
Cisco ASA Backup DHCP & Health-Based Activation
A realistic sample platform for this report is a Cisco ASA 5516-X or Firepower 1010 running ASA software. In this design, the ASA is not a full Windows-style failover partner. It is an emergency responder staged on the inside network and only activated when the Windows server path is unavailable.
- Create the backup pool at 10.40.10.210 through 10.40.10.230.
- Apply gateway, lease values, and outage-mode DNS behavior.
- Keep the ASA DHCP responder inactive by default.
- Enable the backup pool only when 10.40.10.10 is confirmed down.
- Turn the emergency pool off after Windows recovery so DHCP authority returns cleanly to the primary platform.
Sample outage workflow: monitor 10.40.10.10 from the edge, enable backup DHCP when health checks fail beyond threshold, and disable the backup scope when health checks recover and remain stable.
Operations & Recovery
The health-check side of the workflow watches whether the domain controller at 10.40.10.10 is reachable. If reachability fails long enough to meet the outage threshold, the Cisco edge activates the emergency DHCP path so renewing or newly connected wired clients can still obtain valid IP configuration.
Trigger Logic
- Cisco repeatedly probes 10.40.10.10.
- If the failure threshold is met, the emergency DHCP pool is enabled.
- Clients renewing during the outage receive fallback leases from Cisco.
- Once the server is healthy again, the backup pool is disabled and Windows resumes authority.
Runbook Flow
- Confirm 10.40.10.10 is unreachable from the Cisco edge.
- Verify the emergency scope is active.
- Test a wired client for lease issuance and outside internet access.
- Restore the Windows VM or DHCP service and confirm stable response.
- Verify Cisco disables the emergency scope and Windows retakes the primary role.
Testing Checklist
- Simulate a DHCP service stop on Windows.
- Simulate a full Windows VM outage from the Proxmox side.
- Validate emergency lease delivery from the Cisco pool.
- Check whether wired clients keep basic internet reachability.
- Restore Windows and verify clean failback behavior.
Operational truth: Cisco ASA DHCP is effective for emergency continuity, but it does not provide the same day-to-day administrative depth, reservation experience, or Windows-integrated DNS behavior as the primary server.
Risk, Governance & Conclusion
- Primary DHCP outage: new or rebooted devices may lose addressing. Mitigation: Cisco emergency pool keeps leases flowing during the outage.
- False failover activation: confusion if both platforms appear active. Mitigation: threshold-based health checks and separate address pools reduce the blast radius.
- Internal DNS degradation: internet access may survive while internal names fail. Mitigation: restore Windows quickly and document reduced outage-mode capability.
- Operational drift: backup configuration becomes messy over time. Mitigation: keep Cisco emergency-only and fail back to Windows automatically.
What Cisco DHCP Does Less Well: it offers less comfortable day-to-day lease visibility than DHCP Manager, reduces Windows-integrated DNS and reservation depth during outage mode, and is appropriate as a continuity layer rather than the preferred long-term primary service.
- Improvement roadmap: native Windows-to-Windows DHCP failover.
- Expanded Proxmox recovery and host replication.
- Advanced monitoring and event reporting.
- Automated lease and DNS cleanup review.
The final takeaway is that this design delivers a practical outage bridge for a healthcare office: Windows Server 2022 remains the preferred DHCP and DNS platform, Proxmox and UPS posture strengthen the primary path, and Cisco edge DHCP provides a temporary continuity layer when the primary server is down. It is honest about its limits, clear about its purpose, and organized as a professional infrastructure workflow.
Summit Care Multi-Campus Private Network Infrastructure
Fictional Summit Care Medical Clinic mock blueprint covering Cisco Meraki campus VPNs, regional Meraki hubs, Azure VPN Gateway, private campus routing, Azure cloud network configuration, master-leaf campus trusts, Entra SSO, operations, budget planning, benefits, risks, and validation.
Prepared by: Sidiq Daniel
Document style: black-and-white master PDF source
Overview
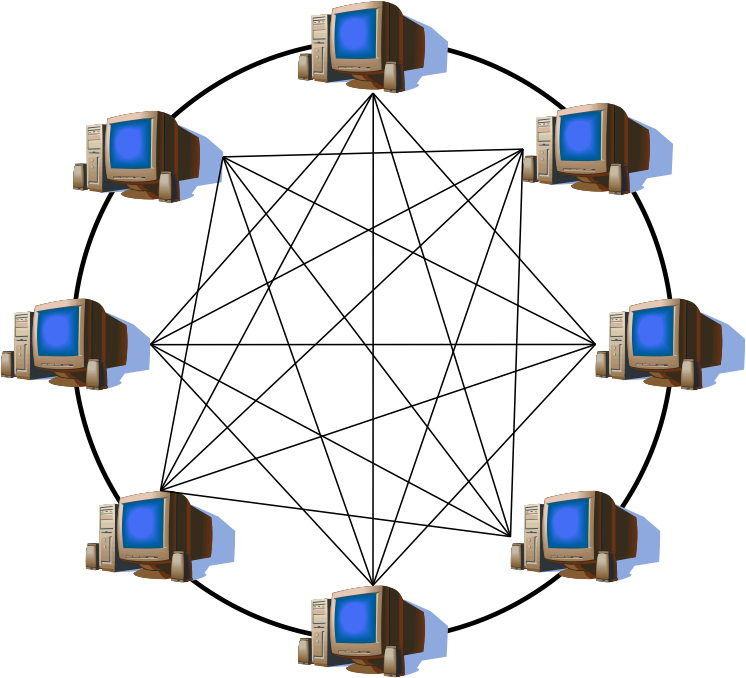
A fictional mock enterprise networking blueprint showing how Summit Care Medical Clinic can connect many campuses through Cisco Meraki Auto VPN, regional Meraki VPN hubs, Azure VPN Gateway, Azure route tables, private cloud services, and controlled sister-campus routing without exposing internal systems to the public internet.
- 10.90.0.0/16 Azure cloud network and gateway VNet.
- 10.91.0.0/16 East regional campus supernet.
- 10.92.0.0/16 West regional campus supernet.
- Hub controlled regional private WAN model.
Master Project Areas
- Overview & Strategy: business reason, regional hub model, campus VPN design, sister-campus communication pattern, and why the network avoids an unmanaged full mesh.
- Architecture & Deployment: Meraki campus setup, regional hub configuration, Azure VPN Gateway, IP planning, route advertisements, firewall rules, and validation checks.
- Operations & Runbooks: monitoring, failover, change control, troubleshooting, packet-flow validation, and route reviews.
- Governance & Cost: budget planning, benefits, risks, compliance controls, operational blockers, and scaling recommendations.
Mock Blueprint Notice
Summit Care Medical Clinic is used only as a virtual company for this infrastructure blueprint. The report does not represent a real healthcare company, real patient environment, real corporate tenant, or real production network. All domains, subnets, campus names, trust paths, and configuration examples are mock design values created for a portfolio-style project.
Purpose
The project turns separate campus LANs into one governed private network fabric. Each campus keeps its local switching, VLANs, wireless, printers, voice, and user services, while Meraki VPN tunnels provide encrypted private paths to nearby regional hubs. Those hubs connect to Azure VPN Gateway so cloud workloads, centralized identity services, management tools, and approved sister-campus systems can communicate across the country.
Core Concept
- Campus Meraki MX Spokes: each campus deploys a Cisco Meraki MX security appliance that advertises local VLANs into Meraki Auto VPN and builds encrypted tunnels to its assigned regional hub.
- Regional Meraki VPN Hubs: nearby cities connect to stronger hub sites such as Queens in the East or Phoenix in the West, concentrating spoke traffic and policy control.
- Azure VPN Gateway: Azure hosts the cloud VPN gateway inside a dedicated GatewaySubnet, allowing hubs to establish site-to-site IPsec tunnels into cloud services.
- Private Routed Fabric: the result behaves like a private WAN where campuses can reach approved sister-campus resources, Azure-hosted systems, monitoring services, backups, and management jump hosts.
Traffic Model
- Campus to Azure: Campus MX to regional hub to Azure VPN Gateway.
- Campus to Sister Campus: Campus MX to regional hub to Azure or inter-hub route to sister-campus hub to sister-campus MX.
- Local Internet: campus MX to local ISP so general browsing does not hairpin through Azure.
- Administration: IT jump host or management subnet to Azure VPN Gateway to regional hub to campus MX/LAN.
Target Outcomes
- Deploy Cisco Meraki MX VPN appliances at every campus edge.
- Group nearby cities behind regional Meraki VPN hubs to reduce tunnel sprawl.
- Connect each regional hub to Azure VPN Gateway using site-to-site IPsec.
- Advertise non-overlapping campus subnets into the private routing fabric.
- Allow approved sister-campus communication through route and firewall policy.
- Provide private cloud routing to Azure-hosted identity, monitoring, backup, and application workloads.
- Design for growth so new campuses can be added through a repeatable template.
Readiness scores: private WAN scalability 93%, campus routing consistency 91%, Azure integration readiness 89%, and operational resilience 86%.
Regional Hub Strategy
The regional hub model reduces tunnel sprawl, creates cleaner operations, provides a policy control point, and makes Azure a cloud-ready headend without removing local campus autonomy.
- Less Tunnel Sprawl: campuses keep a small number of logical VPN relationships while still gaining private reachability.
- Cleaner Operations: IT can inspect hub paths first when multiple nearby campuses lose cloud connectivity.
- Policy Control Point: hubs are natural places to apply VPN firewall rules and control east-west traffic.
- Cloud-Ready Network: Azure VPN Gateway becomes the stable headend for workloads, identity services, jump hosts, monitoring, and backups.
Communication Principles
- No overlapping subnets: every campus receives a unique allocation.
- Least-needed routing: only required prefixes are advertised.
- Firewall before trust: transport does not equal permission.
- Local breakout for internet: general web traffic exits from the local campus ISP.
- Cloud routing documented: Azure local network gateways, route tables, and UDRs are kept current.
Identity Trust And SSO Layer
The private network carries the traffic, but identity decides who can actually sign in. This keeps the master-leaf model: a central cloud-connected master identity domain lives in Azure, each campus keeps its own local domain, and one-way trusts let approved global users authenticate at other campuses without turning every campus into a fully trusted peer.
- Azure master identity domain: SCGLOBAL.LOCAL.
- Microsoft Entra tenant: summitcare.org.
- East campus leaf domains: SCQNS.LOCAL, SCMAN.LOCAL, SCBKLYN.LOCAL, SCNWRK.LOCAL.
- West campus leaf domains: SCPHX.LOCAL, SCDAL.LOCAL, SCDEN.LOCAL, SCLAX.LOCAL.
- Trust direction: campus leaf domains trust SCGLOBAL.LOCAL, but the master domain does not trust them back.
Meraki VPN, Azure Gateway, IP Scheme & Deployment
The design uses a clean private addressing model so every route is predictable: Azure owns 10.90.0.0/16, the East region owns 10.91.0.0/16, and the West region owns 10.92.0.0/16.
- Azure hub VNet: 10.90.0.0/16.
- Azure shared services subnet: 10.90.10.0/24.
- Azure application subnet: 10.90.20.0/24.
- GatewaySubnet: 10.90.254.0/27.
- East regional hub: Queens at 10.91.0.0/24, with Manhattan, Brooklyn, and Newark as spokes.
- West regional hub: Phoenix at 10.92.0.0/24, with Dallas, Denver, and Los Angeles as spokes.
Local Campus Network Build
Every Summit Care campus starts with a clean local LAN before VPN or cloud routing is enabled. The campus network must have predictable VLANs, gateway IPs, DHCP scopes, DNS settings, switch trunks, wireless SSIDs, and management access so Meraki Auto VPN can advertise stable networks into the private WAN.
- Meraki MX edge appliance with dual WAN where available.
- Core switching via Meraki MS or Cisco Catalyst.
- User, voice, server, wireless, guest, and management VLANs.
- Guest VLAN excluded from Auto VPN so it never enters the private network.
Azure VPN Gateway Build
- Create resource group RG-SC-HUB-NETWORK.
- Create SCAZ-HUB-VNET using 10.90.0.0/16.
- Build subnets for identity, shared services, management, applications, and GatewaySubnet.
- Deploy Azure VPN Gateway using a route-based SKU sized for pilot or production.
- Create static public IPs and one local network gateway per regional Meraki hub.
- Create site-to-site VPN connections and attach route tables for 10.91.0.0/16 and 10.92.0.0/16.
Route Advertisement & OSPF Design
Meraki Auto VPN route advertisement handles most campus-to-hub reachability, while Azure local network gateway prefixes provide cloud return paths. OSPF can still be part of local hub or core routing, but is optional and scoped carefully.
- Campus VLANs to MX through static VLAN interfaces or routed core default paths.
- Campus spokes to regional hubs through Meraki Auto VPN.
- Azure to campuses through Azure UDRs pointing to the virtual network gateway.
- East and West route summarization where practical.
Operations, Monitoring, Failover & Runbooks
The national private network is operated through Meraki Dashboard health, Azure VPN metrics, route checks, ISP status, alerting, and user-impact validation.
- Review Auto VPN tunnel health, latency, packet loss, uplink status, and device availability daily.
- Check Azure VPN Gateway tunnel status, throughput, flaps, and health metrics.
- Confirm monitoring collectors can reach key campus infrastructure.
- Track help desk symptoms that map to route changes, ISP degradation, DNS failures, or hub outages.
Failover design includes dual ISP circuits at hubs, warm-spare MX pairs, Azure zone-redundant gateway SKUs, and documented alternate paths such as LTE backup or secondary hub assignment.
Troubleshooting & Validation
- Check campus MX uplinks, Auto VPN status, advertised VLANs, and VPN firewall rules when one campus cannot reach Azure.
- Check hub WAN, non-Meraki VPN tunnels, Azure connection status, and local network gateway prefixes when a region loses cloud reachability.
- Validate route inventory, blocked VLAN tests, sister-campus service access, and hub failover during maintenance windows.
- Validate identity trust with
nslookup, nltest /domain_trusts, and pilot global-user sign-in testing.
Governance, Budget, Benefits & Risks
Budget planning includes Meraki MX appliances, licensing, ISP circuits, Azure VPN Gateway, Azure public IP and logging, implementation labor, and ongoing operations.
- Benefits: private nationwide connectivity, repeatable campus deployment, cloud integration, and operational visibility.
- Risks: regional hub failure, Azure VPN Gateway bottlenecks, overlapping campus subnets, too-broad east-west access, weak shared-key handling, poor documentation, and ISP instability.
- Mitigations: HA MX pairs, dual ISP circuits, right-sized Azure SKUs, central IP registry, least-needed routes, password vaults, and current documentation.
Final Summary
The final design creates a scalable national private network without forcing every campus into a fragile manual tunnel mesh. Each campus uses Cisco Meraki MX as a spoke, nearby cities connect into regional Meraki hubs, the hubs establish secure IPsec tunnels to Azure VPN Gateway, and Azure route tables provide return paths to approved campus prefixes.
This lets sister campuses communicate over private routes, lets Azure-hosted services reach campuses, and gives IT a consistent way to add new sites. The strongest production version includes non-overlapping IP space, hub HA, dual ISP links, Azure zone-redundant VPN Gateway, documented firewall rules, monitored tunnel health, and clear budget ownership for hardware, licenses, cloud gateway cost, circuits, and operations.
Summit Care Windows Server 2022 Enterprise Domain Configuration
This document explains how Summit Care Medical Clinic implemented a practical Windows Server 2022 enterprise domain environment. The project covers Active Directory Domain Services, DNS, DHCP, NPS/RADIUS, AD Certificate Services, WDS, Group Policy, Windows Time, backup domain controllers, Synology NAS storage, Proxmox, Hyper-V, VDI, Task Scheduler automation, Event Viewer, SNMP monitoring, Microsoft Entra hybrid identity, and Microsoft 365 SSO.
Windows Server 2022, AD DS / DNS / DHCP, NPS & AD CS, Proxmox / Hyper-V, and M365 SSO
Project Goal
Build a real enterprise domain control plane for identity, network services, secure access, deployment, backup, monitoring, and remote work in a healthcare clinic environment.
Implementation Focus
Move beyond theory by documenting how each Windows Server feature was implemented, validated, and tied to realistic Summit Care workflows.
Contents
- Overview & Platform Choice
- AD DS, DCs, DNS & Time
- DHCP, WDS, NAS & Backups
- GPO, NPS/RADIUS, Certificates & SSO
- Hypervisors, VDI & Automation
- Final Benefits
Overview & Platform Choice
Summit Care selected Windows Server 2022 because it is stable, widely supported, and well suited for AD DS, DNS, DHCP, NPS, AD CS, WDS, Group Policy, Windows Time, and Hyper-V. Windows Server 2025 may be useful later, but 2022 reduces compatibility risk and avoids early-release bugs during a healthcare infrastructure build.
- Centralize users, computers, groups, service accounts, and policies in Active Directory.
- Provide reliable DNS and DHCP so clients can find domain services and internal tools.
- Use GPOs to secure workstations, deploy certificates, map resources, and enforce baselines.
- Secure office network access with NPS/RADIUS, 802.1X, WPA3-Enterprise, and AD CS.
- Support remote work and testing with VDI, VPN, RDP, Hyper-V, and Proxmox virtual machines.
- Build resilience through a backup domain controller, replication, Synology NAS backups, and scheduled automation.
Active Directory, Domain Controllers, DNS & Windows Time
- SC-DC01: primary domain controller with static IP, AD DS, DNS, DHCP, GPO management, and primary time hierarchy role.
- SC-DC02: backup domain controller with AD DS, DNS, global catalog, replication, and failover authentication support.
- SC-NPS01: NPS/RADIUS server for 802.1X, WPA3-Enterprise, user and device authentication, and RADIUS logging.
- SC-CA01: enterprise certificate authority for computer certificates, NPS certificates, and auto-enrollment.
- SC-WDS01: deployment server for PXE boot, Windows images, and standardized workstation rollout.
Implementation included assigning static IPs, promoting primary and backup domain controllers, validating SYSVOL and NETLOGON, running dcdiag and repadmin /replsummary, configuring DHCP option 006 for dual DNS delivery, and validating Windows Time because Kerberos, certificates, logs, and NPS authentication depend on accurate time.
DNS Records For Internal Services
- dc01 / dc02: domain controller and DNS discovery for reliable authentication and Group Policy access.
- sql.summitcare.local: stable DNS name for database or clinical tool backends.
- intranet.summitcare.local: internal web server or documentation portal.
- nas.summitcare.local: Synology backup and shared storage target.
DHCP, WDS, Synology NAS & Backup Strategy
DHCP provides office clients, VDI systems, printers, phones, and test machines with managed addressing. Critical systems use static addresses or reservations so domain services, NAS storage, RADIUS, WDS, and database tools remain predictable.
- DHCP scope with client pool, exclusions, reservations, router option 003, DNS option 006, and suffix option 015.
- DHCP failover through Windows DHCP failover or documented emergency edge DHCP with non-overlapping pools.
- WDS for PXE boot, boot images, install images, and pilot deployment into a virtual desktop before production rollout.
- Synology NAS joined to the domain, permissioned with AD groups, and used for backups and retained exports.
Backup targets include system state backups for domain controllers, GPMC exports, DHCP configuration and lease exports, AD CS database and CA backups, PowerShell scripts and Task Scheduler exports, and hypervisor VM backups for domain services, VDI, and test machines.
Group Policy, NPS/RADIUS, Certificates & Entra SSO
- Group Policy: password rules, lockout policy, workstation firewall, mapped drives, RDP control, certificate auto-enrollment, and Wi-Fi profiles.
- NPS/RADIUS: RADIUS policies for wireless access points, switches, user groups, computer groups, and approved authentication methods.
- 802.1X / WPA3-Enterprise: domain users and computers authenticate to the office network through NPS.
- AD Certificate Services: enterprise CA, computer certificate templates, NPS server certificate, auto-enrollment GPO, and CRL/AIA planning.
- Microsoft Entra SSO: verified public domain, UPN suffix setup, Entra sync, MFA, and Microsoft 365 app sign-in.
A real GPO scenario in the design has domain computers receiving certificates through auto-enrollment, receiving the secure office Wi-Fi profile through Group Policy, validating the NPS server certificate, and connecting through WPA3-Enterprise / 802.1X without a shared Wi-Fi password.
Proxmox, Hyper-V, VDI, Automation & Monitoring
A type-1 hypervisor allows Summit Care to use one physical server for multiple roles, including domain controllers, NPS, CA, WDS, virtual office desktops, remote work VDI, and sandbox testing. Proxmox hosts the core virtual machines, while Hyper-V and nested virtualization can be used for Microsoft lab testing where supported.
- VDI / Remote Work: remote staff VPN into the network and then RDP into assigned virtual office desktops.
- Sandbox Testing: virtual desktop clients receive GPOs, certificates, DNS, DHCP, and application access before production rollout.
- Task Scheduler: scheduled scripts export DHCP, back up GPOs, run
dcdiag and repadmin, copy outputs to NAS, and export logs.
- Event Viewer: review Directory Service, DNS, DHCP, NPS, certificate enrollment, security, and system logs.
- SNMP Monitoring: monitor switches, APs, NAS, UPS, hypervisor host, and other infrastructure devices.
Final Benefits
The completed Summit Care Windows Server 2022 implementation turns the clinic server environment into a full enterprise platform. Active Directory centralizes identity. DNS makes internal tools discoverable. DHCP gives clients reliable addressing. A backup domain controller protects logon and name resolution. Group Policy secures workstations at scale. NPS/RADIUS and AD CS enable enterprise network authentication and certificates.
WDS standardizes desktop deployment. Synology NAS supports the backup strategy. Proxmox, Hyper-V, and VDI make the hardware flexible for testing and remote work. Task Scheduler, Event Viewer, SNMP, and health checks improve daily operations. Microsoft Entra hybrid identity and UPN alignment connect the local domain to Microsoft 365 SSO. The result is a healthcare network that is easier to manage, easier to recover, and far more secure than unmanaged workgroup computers or shared-password network access.
What Tavernix Represents
Tavernix stands at the intersection of software development, hardware and infrastructure, and business technology solutions. It is built as a unified platform for launching, operating, and scaling real-world systems rather than treating software, infrastructure, and operations as separate tracks.
Software Development
- Custom web platforms and applications.
- Automation systems and internal tools.
- AI-powered solutions such as outbound bots and intelligent workflows.
- API integrations and backend infrastructure.
Hardware & Infrastructure
- Network architecture and deployment.
- Rack-and-stack hardware builds.
- On-site installations and system rollouts.
- Secure and scalable infrastructure design.
Business Technology Solutions
- End-to-end systems for real-world operations.
- Workflow automation to reduce manual labor.
- Customer-facing platforms and service tools.
- Technology strategy aligned with business growth.
Platform Philosophy
Tavernix is built on three core principles: execution over theory, integration over isolation, and scalability by design.
- Execution Over Theory: every solution is designed with deployment in mind and built for live environments.
- Integration Over Isolation: Tavernix focuses on connected systems that communicate, scale, and operate together.
- Scalability by Design: solutions are built with future expansion in mind, from startups to established businesses.
Ecosystem of Projects
- AI & Automation: Hawk 7 AI Security Systems and Destiny Outbound AI Bot.
- Business Platforms: Industry Exams Plus and internal systems for workflow optimization and data handling.
- Service-Based Technology: Computer Repair Queens and client-facing solutions for scheduling, communication, and service delivery.
- Experimental & Development Projects: rapid prototyping environments, startup-style builds, and iterative product development pipelines.
Development Approach
Tavernix follows a structured lifecycle that moves from discovery and planning into design, development, deployment, and ongoing optimization.
- Discovery and planning around business needs, system requirements, and workflow mapping.
- Design and architecture focused on scalable blueprints, integrations, security, and reliability.
- Full-stack development across backend logic, APIs, automation, frontend interfaces, and user experience.
- Deployment covering live rollout, network and infrastructure configuration, and system validation.
- Optimization and iteration through performance improvements, feature expansion, and updates based on real usage.
Use Cases
- Healthcare operations through automation, communication systems, and workflow tools.
- Education platforms through structured learning systems and content delivery.
- Small business infrastructure such as websites, booking systems, and internal tools.
- Security and surveillance through AI-enhanced monitoring systems.
- Service-based businesses through customer management and operational efficiency.
Positioning
Tavernix is not just a development agency, a hosting platform, or a consulting service. It is a hybrid technology engine that combines all three into one unified system.
Vision
The long-term vision for Tavernix is to evolve into a scalable technology ecosystem that powers multiple independent brands and products, enables rapid deployment of new ideas, supports both internal innovation and external clients, and becomes a foundation for future SaaS and enterprise solutions.
Conclusion
Tavernix represents a modern approach to technology, where software, hardware, and business operations are no longer separate but part of a single integrated system. It is a platform built not just to create projects, but to launch, manage, and scale real-world solutions.
Industry Exams Plus
Industry Exams Plus is a structured learning platform designed to help individuals prepare for professional certifications through organized study systems, practice exams, and guided learning resources. It brings together multiple areas of certification-based education into a single, accessible platform, allowing users to move from learning to testing with clarity and direction.
What it represents
Industry Exams Plus represents a shift from scattered study methods to a centralized, system-driven approach to certification preparation.
- A unified platform for exam-focused learning.
- A structured path from study to certification readiness.
- A scalable system supporting multiple industries and subjects.
- A bridge between knowledge acquisition and real-world credentials.
Platform Focus
Practice & Assessment
- Certification-style practice exams.
- Question banks designed to simulate real testing environments.
- Performance tracking and knowledge reinforcement.
Structured Learning
- Organized study materials aligned to certification objectives.
- Clear progression paths across different subjects and levels.
- Support for both beginners and advancing learners.
Multi-Industry Coverage
- Technology certifications.
- Healthcare and allied fields.
- Business and professional development tracks.
- Expandable into additional industries over time.
Learning Approach
Industry Exams Plus is built around a learn, practice, and validate model.
- Learn: users engage with structured content aligned to certification topics.
- Practice: they reinforce knowledge through targeted practice exams and repetition.
- Validate: they assess readiness through simulated testing environments before real exams.
Platform Capabilities
- Web-based learning system accessible across devices.
- Scalable architecture for adding new subjects and exams.
- Continuous content expansion and updates.
- Designed for both independent learners and broader educational use.
Position Within Tavernix
Industry Exams Plus operates as the education and knowledge platform within the Tavernix ecosystem.
- While other Tavernix projects focus on infrastructure, automation, and service delivery.
- Industry Exams Plus focuses on skill development, certification readiness, and user growth through structured learning systems.
Use Cases
- Individuals preparing for certification exams.
- Career changers entering new industries.
- Students seeking structured study support.
- Professionals looking to validate or expand their credentials.
Core Value
- Clarity: structured paths instead of scattered resources.
- Consistency: repeatable learning systems that work.
- Accessibility: learning available anytime, anywhere.
- Progression: guiding users from beginner to certified.
Conclusion
Industry Exams Plus is more than a study tool. It is a learning system designed to produce results. By combining structured content, practical testing, and scalable delivery, it helps users move from uncertainty to confidence, and ultimately, to certification success.
Ubiquiti UniFi WLAN Unification Project
A Summit Care Medical Clinic infrastructure report focused on unifying wireless, routing, VPN, guest access, RADIUS authentication, cloud management, and branch visibility across virtual office locations throughout the five boroughs.
UniFi Cloud Gateway, Cloud Key Gen2, U7 Pro XL Access Points, and Windows Server NPS/RADIUS
Purpose & Goal
Build one supportable UniFi operating model for Summit Care offices so wireless access, routing, VPN, monitoring, guest access, and provisioning can be managed consistently from a cloud-connected dashboard.
Design Principle
Keep network access centralized through UniFi while using Windows Server Active Directory and NPS/RADIUS for identity-based staff wireless authentication.
Table of Contents
- Executive Summary
- Overview & Strategy
- Architecture & Configuration
- Operations, VPN & Monitoring
- Risk, Governance & Conclusion
Executive Focus
This project is designed to prove that Ubiquiti UniFi can give Summit Care Medical Clinic one repeatable platform for branch routing, secure staff Wi-Fi, guest access, cloud monitoring, remote provisioning, VPN, and wireless coverage across many offices throughout the five boroughs.
- Unified Management: Cloud Key Gen2 hosts UniFi Network so IT can adopt devices, see topology, monitor clients, push SSIDs, update firmware, and manage sites through local private access or
unifi.ui.com.
- Enterprise Staff Wireless: Staff Wi-Fi authenticates through Windows Server NPS/RADIUS using UDP 1812 for authentication and UDP 1813 for accounting, tying access to Active Directory users and groups.
- Guest Isolation: Guest Wi-Fi uses a separate VLAN, subnet, firewall policy, and UniFi captive portal so patients and visitors receive internet access without reaching internal clinic resources.
Important design note: this is a WLAN unification and cloud management project, not just an access point installation. The value comes from tying routing, wireless, RADIUS, guest policy, VPN, monitoring, and provisioning into one repeatable UniFi model.
Overview & Strategy
Summit Care needed a consistent way to manage wireless and network access across multiple clinic offices. UniFi provides the common controller, gateway, wireless, VPN, and monitoring layer, while Windows Server on Proxmox continues to provide domain identity and RADIUS policy.
- Unify multiple Summit Care offices under one UniFi management experience.
- Deploy U7 Pro XL access points with consistent SSIDs, VLANs, and roaming behavior.
- Use Windows Server NPS/RADIUS for secure staff wireless authentication.
- Separate staff, guest, management, clinical, and VPN traffic with VLANs and firewall rules.
- Support private GUI access by management IP and remote access through
unifi.ui.com.
Readiness snapshot: centralized UniFi visibility 96%, staff wireless authentication strength 92%, guest isolation maturity 90%, and remote support efficiency 94%.
Summit Care UniFi Blueprint Snapshot
- UniFi Cloud Gateway: edge router and security gateway for routing, VLAN boundaries, VPN, and branch connectivity.
- UniFi Cloud Key Gen2: UniFi Network controller for adoption, monitoring, configuration, firmware, remote access, and backup workflows.
- Ubiquiti U7 Pro XL access points: Wi-Fi 7 access layer providing high-capacity coverage for staff, clinical, guest, and mobile devices.
- Dell PowerEdge R740xd with Proxmox: virtualization host running Windows Server domain controller and NPS/RADIUS services.
Architecture & Configuration
The technical build centers on three layers: the UniFi gateway for routing, firewalling, VLANs, and VPN; the Cloud Key Gen2 for network management; and Windows Server NPS/RADIUS for staff identity authentication.
Core Network Design
- Management VLAN 10 / 10.10.10.0/24 for Cloud Key, gateway, switches, AP management, and administrator interfaces.
- Staff Wi-Fi VLAN 20 / 10.20.20.0/24 for domain-authenticated employee devices.
- Clinical devices VLAN 30 / 10.30.30.0/24 for approved clinic systems and office equipment.
- Guest Wi-Fi VLAN 40 / 10.40.40.0/24 for internet-only access through captive portal controls.
Cloud Key Gen2 Setup
- Connect the Cloud Key Gen2 to the management network and reserve a private management IP.
- Open the local GUI for first-time setup and controller hardening.
- Link authorized cloud access through
unifi.ui.com and require protected admin accounts.
- Update firmware, create site naming standards, configure backups, and adopt UniFi devices.
Windows NPS/RADIUS Setup
- Install Network Policy Server on the Windows Server VM running on Proxmox.
- Register NPS in Active Directory and create policies for approved Summit Care staff groups.
- Add UniFi infrastructure as RADIUS clients with shared secrets.
- Permit UDP 1812 and UDP 1813 between UniFi and Windows Server.
- Enable certificate-based 802.1X access, such as EAP-TLS or PEAP with certificate validation, for managed devices.
Certificate-based access strengthens the staff SSID by validating the device, not just the person typing a password. Guest portal and wireless mesh are also part of the build, with guest access isolated on its own VLAN and a second-floor U7 Pro XL able to uplink wirelessly where cabling is unavailable.
Operations, VPN & Monitoring
Summit Care can manage UniFi locally through private management addresses or remotely through unifi.ui.com. VPN access gives authorized administrators a secure path back into approved internal networks without exposing management interfaces directly to the internet.
- Private GUI Access: administrators can open the Cloud Key or gateway by private IP while on site or connected through VPN.
- Cloud Access: UniFi cloud access provides remote visibility into offices, devices, clients, alerts, topology, firmware, and adoption state.
- VPN Access: the UniFi gateway provides VPN connectivity using Teleport, WireGuard, or L2TP/IPsec based on support needs.
Operational Runbook
- Open UniFi Network through
unifi.ui.com or the private controller address.
- Review gateway health, WAN status, AP status, switch uplinks, VLAN assignment, and client experience.
- For staff Wi-Fi issues, verify RADIUS reachability to Windows Server NPS on UDP 1812 and UDP 1813.
- For guest issues, test captive portal load, guest VLAN addressing, DNS, firewall restrictions, and internet egress.
- For mesh issues, review wireless uplink quality, retries, channel utilization, and second-floor AP placement.
Risk, Governance & Conclusion
- RADIUS or domain controller outage: staff may be unable to authenticate to enterprise Wi-Fi. Mitigation: monitor NPS, protect the Windows Server VM, and document fallback access.
- Guest VLAN leakage: visitors could reach internal clinic assets. Mitigation: explicit deny rules from guest to private networks and segmentation testing.
- Cloud admin account compromise: remote UniFi settings could be changed maliciously. Mitigation: require MFA, least privilege, admin review, and sensitive-change alerting.
- Mesh uplink weakness: second-floor performance may drop if backhaul quality is poor. Mitigation: monitor uplink quality and add Ethernet cabling when feasible.
Final summary: the project demonstrates a complete UniFi WLAN unification design for Summit Care Medical Clinic. The UniFi gateway provides routing, security, and VPN; the Cloud Key Gen2 provides the management plane; U7 Pro XL access points deliver the wireless layer; Windows Server NPS connects staff Wi-Fi to domain identity and certificate-based access; and VLANs, guest portal controls, cloud monitoring, and mesh uplinks make the design practical across real clinic offices in the five boroughs.
Computer Repair Queens
Computer Repair Queens is a service-driven technology initiative focused on delivering fast, reliable, and hands-on support for everyday devices and real-world technical problems. Built with a practical, customer-first mindset, it bridges the gap between traditional repair services and modern tech support by combining on-site service, structured workflows, and dependable execution.
What it represents
Computer Repair Queens represents a real-world application of technical skill, where troubleshooting, repair, and customer interaction come together in a consistent and scalable service model.
- A hands-on approach to solving device and network issues.
- A local-first service model focused on trust and reliability.
- A structured system for delivering repeatable, high-quality support.
- A bridge between technical expertise and everyday user needs.
Service Focus
Device Repair & Troubleshooting
- PCs, laptops, and custom-built systems.
- TV and display-related issues.
- General hardware diagnostics and repair.
- Performance optimization and system cleanup.
On-Site & Local Support
- In-person troubleshooting and resolution.
- Home and small business service calls.
- Real-time problem solving without dependency on remote-only tools.
Technical Support Systems
- Structured intake and issue tracking.
- Clear communication and expectation setting.
- Efficient resolution workflows designed for speed and clarity.
Operational Approach
Computer Repair Queens is not just about fixing devices. It is about delivering a consistent service experience.
- Rapid Diagnosis: quick identification of the issue using practical troubleshooting methods.
- Clear Resolution Path: transparent explanation of the problem and the solution.
- Hands-On Execution: direct repair, replacement, or optimization performed efficiently.
- Customer-Focused Delivery: ensuring the end user leaves with a working system and confidence in the service.
Position Within Tavernix
Computer Repair Queens operates as the service and field-operations arm of the broader Tavernix ecosystem.
- While Tavernix focuses on software development, AI systems, and infrastructure deployment.
- Computer Repair Queens focuses on direct user interaction, physical device repair, and real-world problem solving.
- Together, they represent both digital and physical execution of technology solutions.
Use Cases
- Home users needing fast device repair.
- Small businesses requiring reliable tech support.
- Clients needing in-person troubleshooting over remote assistance.
- Situations where hands-on work is more effective than software-only solutions.
Core Value
- Reliability: problems get solved, not delayed.
- Transparency: clear communication, no guesswork.
- Execution: real fixes, not temporary patches.
- Trust: a service people can depend on locally.
Conclusion
Computer Repair Queens represents the foundation of practical technology work, where real devices, real problems, and real people meet. It transforms technical knowledge into tangible results, delivering dependable solutions in environments where they matter most.
Destiny Outbound AI Bot
Destiny is a multi-channel outbound automation platform designed to handle high-volume communication workflows across businesses of any industry. It transforms traditional outreach, including calls, texts, emails, and notifications, into a fully automated, scalable system capable of operating continuously with speed, consistency, and precision.
Originally conceptualized for healthcare, Destiny has evolved into a universal outbound communication engine adaptable to any business that relies on client interaction, follow-ups, or lead engagement.
What it represents
Destiny represents the shift from manual outreach to intelligent, automated communication systems.
- A scalable outbound communication infrastructure.
- A replacement for repetitive, human-driven outreach tasks.
- A system that increases speed, consistency, and operational efficiency.
- A platform capable of handling thousands of interactions simultaneously.
Core Capabilities
Multi-Channel Outreach
- AI-powered outbound phone calls.
- SMS messaging and automated text workflows.
- Email communication and follow-up sequences.
- SNMP and system-level notifications for infrastructure environments.
- Expandable to additional communication channels as needed.
Automation & Workflow Control
- Predefined outreach sequences and campaigns.
- Trigger-based messaging using events, actions, and time-based logic.
- Smart routing and response handling.
- Continuous operation without manual intervention.
Scalability
- Handles high-volume outbound campaigns.
- Supports growing business communication demands.
- Designed for both small operations and enterprise-level usage.
Use Cases
- Lead Generation & Sales Outreach: automated contact with potential customers at scale.
- Appointment Reminders & Follow-Ups: reducing no-shows and improving engagement.
- Customer Re-Engagement Campaigns: reaching inactive or past clients.
- Operational Notifications: system alerts, updates, and automated communication triggers.
- Service-Based Businesses: managing inbound and outbound communication flow without staffing overhead.
Operational Impact
Destiny replaces repetitive communication workflows that traditionally require call center staff, manual follow-ups, and time-consuming outreach processes with automated execution, consistent messaging, 24/7 availability, and reduced operational costs.
Position Within Tavernix
Destiny operates as the automation and communication engine within the Tavernix ecosystem.
- While other Tavernix projects focus on infrastructure, platforms, and physical deployment.
- Destiny focuses on scalable communication systems, automation of human-driven processes, and business growth through outreach efficiency.
Platform Philosophy
- Efficiency: eliminate repetitive manual work.
- Consistency: deliver the same quality of communication every time.
- Scalability: grow without increasing operational overhead.
- Flexibility: adapt to any industry or workflow.
Conclusion
Destiny Outbound AI Bot is more than an automation tool. It is a communication infrastructure layer for modern businesses. It enables organizations to move faster, reach more people, and operate more efficiently by turning outreach into a system rather than a task.
Hawk 7 AI Security Cameras
Hawk 7 AI Security Cameras is an advanced surveillance platform that transforms traditional camera systems into intelligent, AI-powered monitoring environments. It combines modern computer vision, real-time analytics, and structured deployment practices to deliver smarter detection, faster response, and more reliable security operations for businesses.
Built under the Tavernix ecosystem, Hawk 7 represents the evolution of surveillance from passive recording to active, decision-driven security systems.
What it represents
Hawk 7 represents the shift from standard CCTV systems to AI-enhanced security infrastructure.
- Intelligent monitoring instead of passive recording.
- Real-time detection of people, objects, and events.
- Automated alerts and actionable insights.
- A scalable platform for modern business security needs.
Core Capabilities
AI-Powered Detection
- Human detection and tracking.
- Object recognition and classification.
- Vehicle identification and movement tracking.
- License plate recognition through LPR and ANPR systems.
Smart Event Analysis
- Motion filtering to reduce false positives.
- Behavioral pattern recognition.
- Event-based alerts instead of continuous noise.
- Zone-based detection and monitoring logic.
Real-Time Alerts & Monitoring
- Instant notifications for critical events.
- Integration with mobile, desktop, or centralized dashboards.
- Configurable alert thresholds and escalation paths.
System Architecture
Hawk 7 is designed as a layered security system that combines hardware and software.
- Camera Layer: IP-based surveillance cameras with high-resolution video capture and network streaming.
- Processing Layer: AI inference engines for real-time video analysis, using edge or server-based processing depending on deployment scale.
- Application Layer: monitoring dashboards, user interfaces, alerting systems, event logs, and integration with external systems when required.
Deployment & Infrastructure
Hawk 7 is not just software. It includes real-world deployment execution.
- Camera installation and positioning strategy.
- Structured cabling and network integration.
- On-site system configuration and optimization.
- Secure network segmentation and access control.
This ensures that AI capabilities are backed by reliable physical infrastructure.
Use Cases
- Commercial Security Systems: offices, retail spaces, and operational facilities.
- Property Monitoring: buildings requiring continuous intelligent surveillance.
- Access Control & Entry Monitoring: license plate tracking and controlled entry points.
- Operational Oversight: monitoring workflows, movement, and activity patterns.
Position Within Tavernix
Hawk 7 operates as the AI-powered surveillance and physical security division within Tavernix.
- While other Tavernix projects focus on software platforms, automation systems, and business infrastructure.
- Hawk 7 focuses on real-world security environments, AI-driven monitoring and detection, and end-to-end deployment from hardware to software.
Technical Approach
- Accuracy: minimizing false positives through intelligent filtering.
- Performance: real-time processing with minimal latency.
- Scalability: from small deployments to multi-site systems.
- Security: protected data streams and controlled access.
Core Value
- Smarter Surveillance: systems that understand what they see.
- Operational Efficiency: reduced need for constant human monitoring.
- Faster Response Times: actionable alerts instead of raw footage.
- Modern Security Infrastructure: built for today’s environments.
Conclusion
Hawk 7 AI Security Cameras transforms traditional surveillance into a proactive security system. By combining AI detection, structured deployment, and scalable architecture, it enables businesses to move from simply recording events to actively understanding and responding to them in real time.